"Free"Government Money Scam
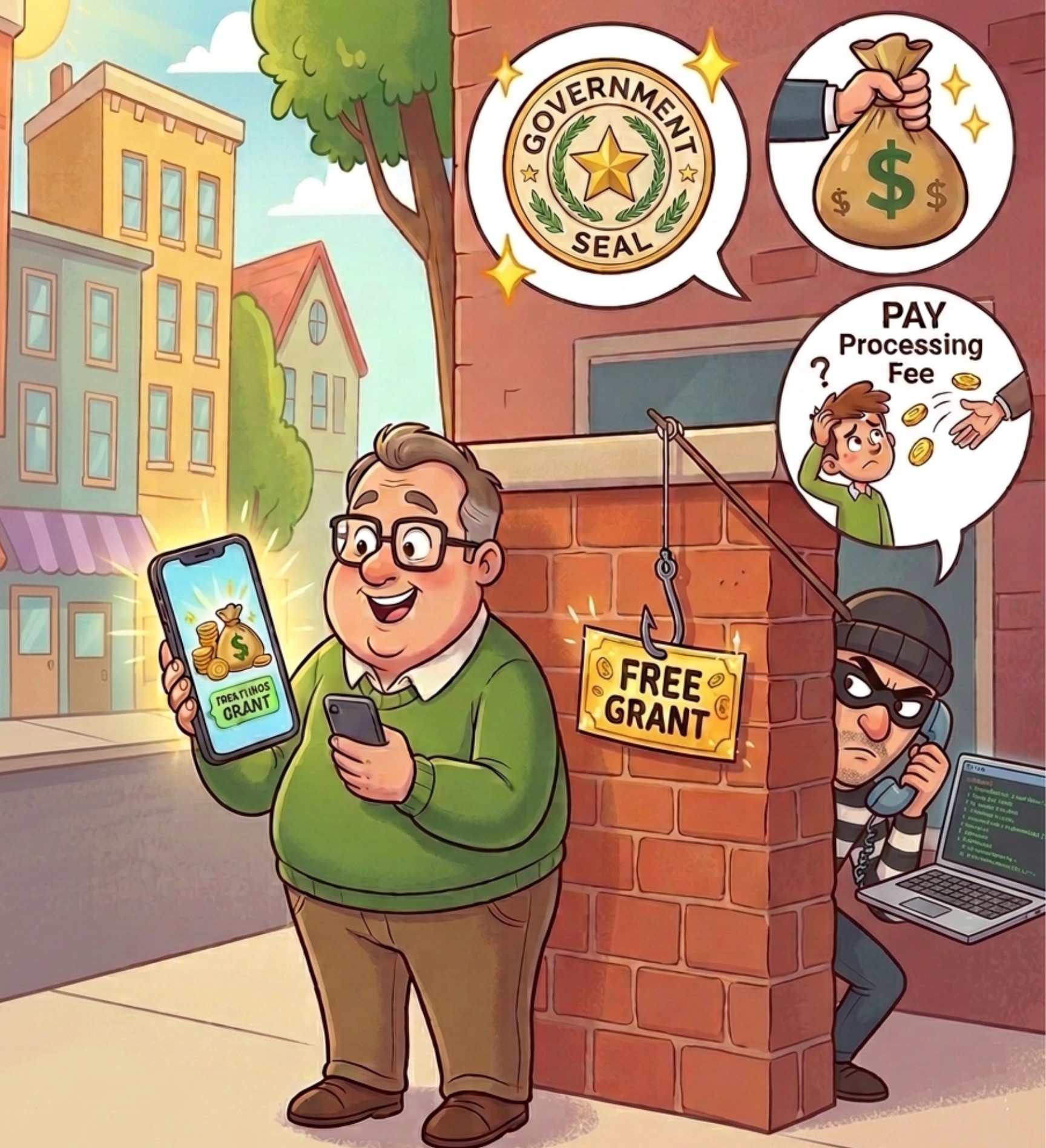 The Federal Trade Commission recently issued an alert concerning a resurgence of fraudulent activity involving "free government grants." Scammers currently utilize social media and text messages to reach potential victims, promising significant sums of money for personal expenses such as home repairs, medical bills, or general financial relief.
The Federal Trade Commission recently issued an alert concerning a resurgence of fraudulent activity involving "free government grants." Scammers currently utilize social media and text messages to reach potential victims, promising significant sums of money for personal expenses such as home repairs, medical bills, or general financial relief.
- Read more about "Free"Government Money Scam
- Log in to post comments

 I previously posted an article about the
I previously posted an article about the  First of all, there is no such thing as Google Coin. The Google Coin AI story is yet another in a long line of cryptocurrency investment scams, leveraging the high-pressure tactics of the "crypto craze" to exploit unsuspecting investors.
First of all, there is no such thing as Google Coin. The Google Coin AI story is yet another in a long line of cryptocurrency investment scams, leveraging the high-pressure tactics of the "crypto craze" to exploit unsuspecting investors.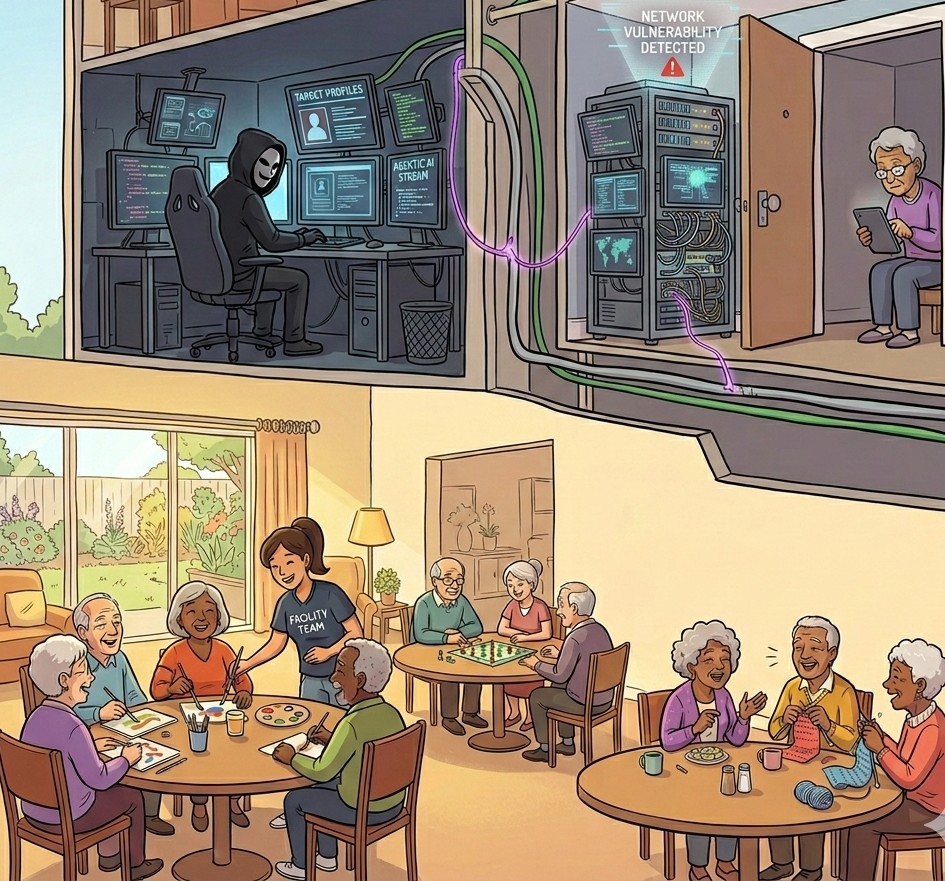 I was just reading
I was just reading  Video conferencing has now been added to the tactics used in police personation scams, representing a growing trend in cybercrime where fraudsters impersonate law enforcement officers to manipulate victims through psychological pressure.
Video conferencing has now been added to the tactics used in police personation scams, representing a growing trend in cybercrime where fraudsters impersonate law enforcement officers to manipulate victims through psychological pressure. Once the exclusive domain of international espionage and Hollywood Spy Movies, rogue mobile towers have officially moved into the hands of street-level criminals. For decades, "Stingrays" were high-budget tools used by actual spies to intercept communications of high-value targets.
Once the exclusive domain of international espionage and Hollywood Spy Movies, rogue mobile towers have officially moved into the hands of street-level criminals. For decades, "Stingrays" were high-budget tools used by actual spies to intercept communications of high-value targets. Awhile back I wrote an article on how
Awhile back I wrote an article on how 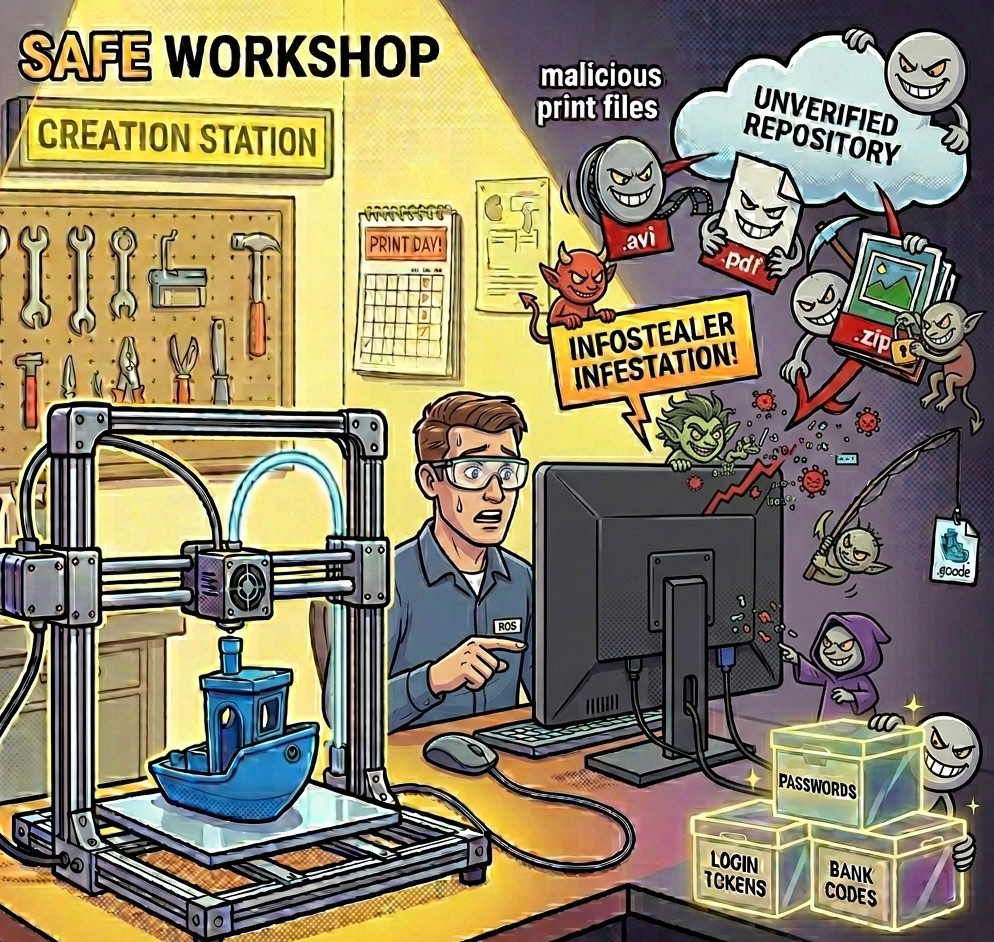 The 3D printing community relies on a culture of open sharing. Whether seeking a replacement part or a complex artistic model, users frequently download files from various repositories and forums. However, opportunistic criminals now exploit this trust by turning seemingly harmless hobbyist files into delivery vehicles for malicious software.
The 3D printing community relies on a culture of open sharing. Whether seeking a replacement part or a complex artistic model, users frequently download files from various repositories and forums. However, opportunistic criminals now exploit this trust by turning seemingly harmless hobbyist files into delivery vehicles for malicious software.